Education
Your Guide to Multisig Wallet Security for Bitcoin Inheritance
Secure your legacy with our complete guide to the multisig wallet. Learn how to protect assets, prevent loss, and create a seamless Bitcoin inheritance plan.
A standard crypto wallet is like a digital safe with a single key. It's a simple setup, but it comes with a significant vulnerability. If that key is lost, stolen, or damaged, the contents are either gone forever or vulnerable to theft.
This creates what security experts call a single point of failure, a lone vulnerability that can trigger a total loss. A staggering number of crypto assets have been lost precisely this way. A multisig wallet provides a robust solution to this problem.
What Is a Multisig Wallet?
A multisig (short for multi-signature) wallet is like a high-security bank vault that requires more than one key to open. Instead of a single private key controlling your Bitcoin, this type of wallet demands two or more independent approvals before any funds can be moved. This shared control mechanism is a cornerstone of modern digital asset security.

It operates on an “m-of-n” scheme, where ‘n’ is the total number of keys created and ‘m’ is the minimum number of keys required to approve a transaction. For example, in a popular 2-of-3 setup, three keys exist, but only two are needed to move funds.
Eliminating the Single Point of Failure
This distributed authority model provides powerful protection against a wide range of common risks. By removing the reliance on one person, one device, or one secret, a multisig wallet makes your assets more resilient.
The key benefits include:
Theft Protection: A thief would need to compromise multiple keys, often stored in different locations, making a successful attack exceptionally difficult.
Loss Prevention: If you accidentally lose one key, you can still access your funds using the others. This provides a crucial backup that single-key wallets cannot offer.
Enhanced Inheritance Planning: It allows you to create a robust plan where keys can be distributed among family members, lawyers, or trusted third parties. This ensures your assets can be recovered, a topic we explore further in our guide on the hidden risks of Bitcoin inheritance.
By distributing approval authority, multisig wallets create a natural checkpoint system that stops any one person from moving funds alone. It replaces single-key vulnerability with shared, verifiable control.
From Corporate Vaults to Family Security
Initially, multisig technology was primarily used by large institutions like cryptocurrency exchanges to secure billions in customer funds. The need for robust internal controls and defence against sophisticated hacks made it an essential tool. Today, the number of enterprise-grade multisig wallets in use is in the millions and growing.
However, as Bitcoin's value has grown, individuals and families are realising that they face similar risks. A personal crypto holding can represent a significant portion of a family's net worth, making robust security and clear inheritance planning essential.
The same technology that protects institutional treasuries is now becoming a standard for personal wealth preservation. To fully appreciate its importance, it helps to consider blockchain's role in the future of law. The principles of verifiable, distributed trust are fundamentally changing how we think about ownership and legacy.
Let's now explore how multisig technology works to protect your crypto.
How Multisig Actually Protects Your Crypto Assets
If you're using a standard crypto wallet, you're living with its greatest weakness: a single point of failure. Everything hinges on one private key. That means one mistake, a lost phone, a stolen recovery phrase, or a single click on a phishing link can lead to a total, irreversible loss of your funds. There’s no room for error.
A multisig wallet completely rewrites this security model by introducing shared control. Instead of one key holding all the power, it distributes authority across several keys. This is all made possible by a cryptographic rule called an "m-of-n" signature scheme.
Understanding the M-of-N Signature Scheme
The "m-of-n" model is the core of a multisig wallet. It's simpler than it sounds. Here, 'n' is the total number of keys your wallet has, and 'm' is the minimum number of those keys needed to approve any transaction.
A 2-of-3 setup is a popular and effective choice:
n = 3: You create a total of three keys for your wallet.
m = 2: Any two of those three keys are required to sign off on a transaction.
This simple rule creates an incredibly powerful security checkpoint. No single key can move funds on its own. It's a system that enforces shared control at the protocol level, moving you away from blind trust and into a world of verifiable, cryptographic agreement.
By requiring multiple, independent approvals, a multisig wallet transforms security from a single, fragile point of failure into a distributed, resilient network. It ensures no single person, device, or secret holds absolute power over your Bitcoin.
It's no surprise this approach is gaining momentum. The global multisignature wallets market, currently valued at $1.27 billion, is projected to reach $4.37 billion by 2033. This growth is driven by institutional funds increasingly adopting multisig to manage their treasuries in a compliant manner. You can dig into more data on this trend and learn about the rising adoption of crypto wallets across the UK and Europe.
Building Practical Trust Models
The true value of a multisig wallet is realised when you pair the technology with a well-thought-out trust model. It isn't just about having multiple keys; it’s about strategically distributing them to counter real-world threats. This is where you can apply a security professional's mindset.
Let’s walk through a practical 2-of-3 setup for someone who wants strong personal security and a straightforward recovery plan.
Key 1 (Your Primary Key): You'll keep this on your main hardware wallet, the one you use to initiate transactions. This device stays with you for day-to-day management.
Key 2 (Your Backup Key): This key lives on a second hardware wallet, stored securely in a different location like a safe at home or the office. Think of it as your personal backup in case your primary device is lost, stolen, or broken.
Key 3 (The Failsafe Key): This one is held by a trusted third party—perhaps a close family member, your solicitor, or even in a bank's safe deposit box. This key is your ultimate lifeline against a disaster, a coercion attempt, or simply forgetting where you hid your backup.
This kind of setup protects you from several threats at once. If a thief grabs your primary hardware wallet, they can't move funds with just one key. If you misplace your backup, you can still access your funds using your primary key and the failsafe key. You can explore more about structuring your ownership in our detailed guide on the Bitcoin ownership journey with multisig.
This distributed model gives you layers of defence that a single-signature wallet cannot match, offering genuine peace of mind.
Choosing the Right Multisig Setup for Your Family
Picking the right security model for your digital assets is a personal decision. There’s no single "best" answer. The goal is to find a multisig wallet configuration that fits your specific circumstances, your comfort with risk, and your long-term plans. It's about striking the right balance between robust security, day-to-day convenience, and a clear recovery plan for your family.
This is a critical decision point for any serious crypto holder. The visual below lays out the choice clearly: you can either stick with a high-risk, single-key wallet or upgrade to a low-risk multisig setup.
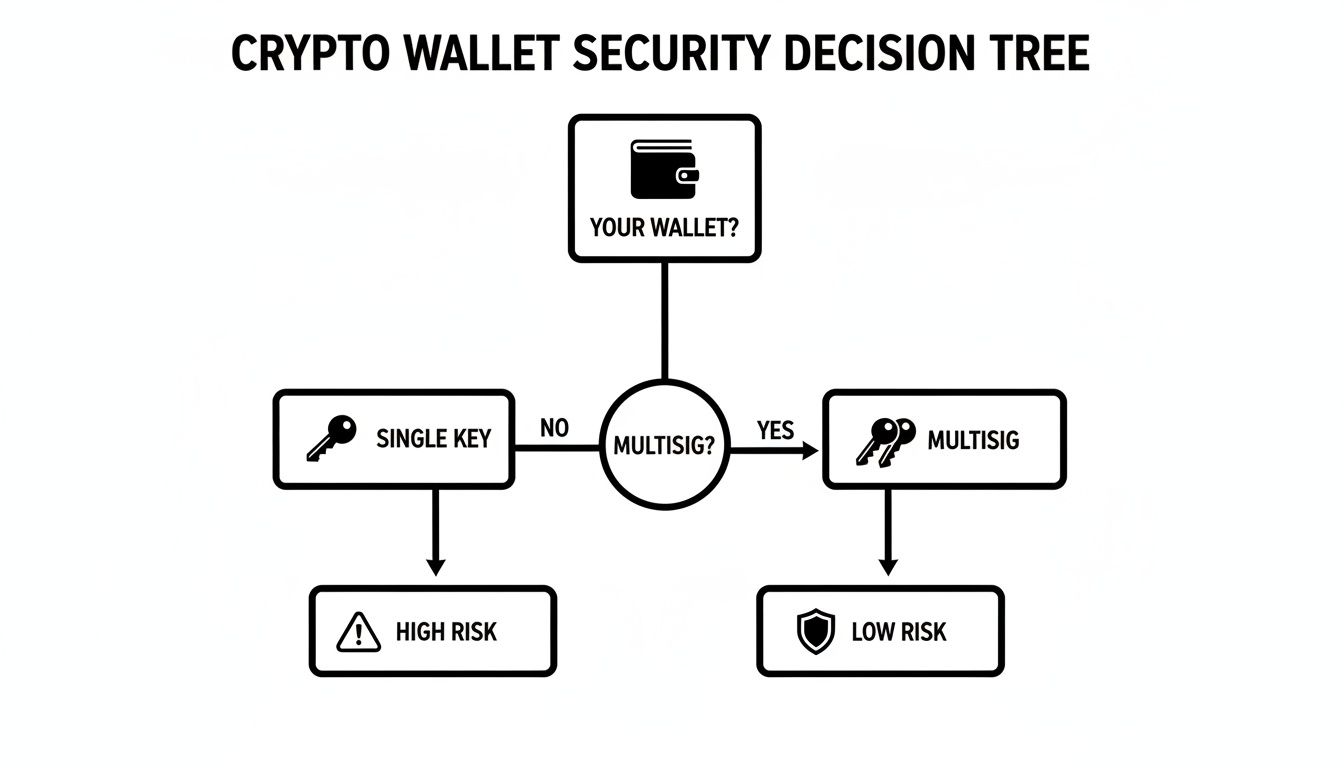
As you can see, a single key might feel simple, but it creates a significant single point of failure. A multisig wallet, on the other hand, builds a fundamentally more resilient foundation for your security.
Comparing Common Multisig Policies
The most popular multisig wallet setups you'll come across are the 2-of-3 and 3-of-5 policies. Understanding the distinct advantages and trade-offs of each is the first step toward building a system that gives you confidence. Your choice will define how your assets are controlled, backed up, and eventually, passed on to the next generation.
A 2-of-3 setup is an excellent starting point, often ideal for an individual or a couple. It offers a great blend of powerful security and practical redundancy. In this model, you create three keys but only need two of them to authorise a transaction.
This means you can lose a key—or have one stolen—and still retain complete control of your funds. It's an effective defence against simple accidents, device failure, or theft.
By contrast, a 3-of-5 policy is built for collaboration and distributed trust. This makes it a natural fit for larger families, business partnerships, or small organisations. With five keys in total, you need three to sign off on any transaction. This setup gives you even greater redundancy (you can lose up to two keys) while demanding broader consensus for any action.
The core difference really boils down to individual control versus group consensus. A 2-of-3 setup prioritises personal recovery, while a 3-of-5 policy prioritises shared governance and resilience against multiple points of failure.
This choice is foundational, as it has a direct impact on your family’s ability to manage the assets if something happens to you. To understand why this is so important, it's worth asking yourself: is your family covered if something happens to you?.
Mapping Configurations to Real-World Scenarios
To make this more concrete, let's explore how these policies work in the real world. The right choice often becomes much clearer when you connect the technical details to your actual life.
Comparing Common Multisig Wallet Configurations
This table breaks down the most common multisig policies to help you see the trade-offs at a glance.
Policy (m-of-n) | Security Level | Redundancy (Keys that can be lost) | Ideal Use Case | Potential Drawback |
|---|---|---|---|---|
2-of-3 | High | 1 key | Individuals, couples, or small business partners. Great for inheritance planning. | One key held by a third party could collude with a thief who steals another key. |
3-of-5 | Very High | 2 keys | Larger families, business partnerships, DAOs, or small organisations. | More complex to set up and manage. Requires coordination between more people. |
2-of-2 | Medium | 0 keys | A simple joint account where both parties must agree to spend. | No redundancy. If one key is lost, the funds are lost forever. High risk. |
1-of-3 | Low | 2 keys | A "spending" wallet where convenience is more important than security. | Anyone with a single key can access the funds. Not recommended for storing significant value. |
Thinking through these options helps you move from abstract concepts to a practical plan.
Scenario 1: The Individual Investor (2-of-3)
Goal: Protect personal Bitcoin holdings from theft and loss, while creating a simple recovery path.
Key Distribution:
Key 1: On your primary hardware wallet for everyday access.
Key 2: On a backup hardware wallet, kept in a home safe.
Key 3: With a trusted third party, like a solicitor or a close relative, along with clear instructions.
Benefit: You can access funds even if you lose your main device or your home safe is compromised. That third key acts as a vital failsafe for inheritance or emergency recovery.
Scenario 2: The Family Joint Account (3-of-5)
Goal: Manage a shared pool of assets where decisions require group agreement, with a robust inheritance plan.
Key Distribution:
Key 1 & 2: Held by the primary partners (e.g., you and your spouse).
Key 3: Held by an adult child or designated heir.
Key 4: Entrusted to the family’s solicitor.
Key 5: Stored in a bank's safe deposit box.
Benefit: No single person can move funds on their own, enforcing collaborative control. It also provides outstanding redundancy, ensuring the family can recover the assets even if two key holders become unavailable.
Ultimately, choosing your multisig policy is less about finding the technically "perfect" solution and more about designing a system that works for your human reality. By thinking through these scenarios, you can confidently build a setup that secures your assets today and protects your family’s future tomorrow.
Creating Your Bitcoin Inheritance Plan Step by Step

Now let's move from theory to action. Your multisig wallet is the technical foundation of a solid Bitcoin inheritance plan, but technology alone is not enough. The key lies in bridging the gap between its cryptographic security and the human process of settling an estate.
A successful plan means your family can take control of your assets smoothly, without needing a deep understanding of security engineering. It’s about creating simple, non-technical instructions that your executor can follow with confidence. This is where smart planning and secure technology come together.
Step 1: Strategically Assign Your Keys
First, you need to distribute the keys from your multisig setup thoughtfully. This isn’t just a security exercise; it’s about creating a clear and deliberate path for recovery. The aim is to ensure no single person has total control, but your chosen group can come together and act when the time comes.
For a common 2-of-3 setup, a robust inheritance model might look like this:
Key 1 (Your Key): You hold this key for managing your funds day-to-day.
Key 2 (Heir's Key): This goes to your primary heir or a trusted family member. It's crucial they understand their role is collaborative, not unilateral.
Key 3 (Advisor's Key): Entrust this key to a neutral third party, like your solicitor or a technical advisor. This person acts as both a failsafe and a guide for the entire process.
This distribution creates a powerful system of checks and balances. Your heir can’t act alone, and neither can the advisor. It's a simple way to protect the estate from rash decisions or internal disputes. When crafting an inheritance plan for digital assets, getting sound legal advice is paramount, which often means consulting with dedicated will and trust lawyers.
Step 2: Create Simple, Non-Technical Instructions
It is important to understand that your family and executor do not need to understand Bitcoin's technical details. What they need is a simple, actionable 'how-to' guide. Avoid technical jargon and focus on clear, procedural steps that anyone can follow.
Your instructions should answer three basic questions:
Who holds the keys? List the names and contact details for each key holder.
Where are the keys? Give general locations for each key (e.g., "in a home safe" or "with our family solicitor"). No need for specifics that could compromise security.
What tool is used? Name the specific multisig wallet software required to coordinate the signatures.
This approach turns a complex cryptographic process into a manageable checklist. It empowers your executor to coordinate the key holders without getting lost in technical details they don't need to know.
The goal of your inheritance instructions is not to teach your family cryptography. It is to give them a simple 'treasure map' that leads them to the right people and the right tools to securely recover your assets.
This level of planning is more important than ever. In the UK, we've seen a surge in crypto adoption alongside the rise of secure self-custody. With Europe projected to have 140 million crypto wallets by 2026, the UK's contribution is significant. A notable 57% of UK adults already use mobile wallets for payments, showing a growing comfort with digital tools. This trend is spilling into crypto, where a multisig wallet provides the serious security needed for wealth preservation and inheritance.
Step 3: Prepare a Digital Asset Schedule
Your standard will is great for listing property and bank accounts, but it's often ill-suited for digital assets. The missing piece of the puzzle is a Digital Asset Schedule. Think of this as a companion document to your will, giving your executor the specific information needed to manage your Bitcoin.
This schedule is not the place for private keys or passwords. Instead, it should contain:
The names of the key holders and their designated roles.
The multisig policy (e.g., "A 2-of-3 signature scheme is in place").
The location of your non-technical instruction letter.
Contact information for a trusted technical advisor who can assist the executor.
By formally documenting this information, you provide crucial legal and procedural clarity. This simple step minimises the risk of family disputes, prevents your executor from getting stuck, and dramatically reduces the chance of your assets being lost forever. We explore this in more detail in our article on why your UK will isn't enough for crypto inheritance).
By combining your multisig wallet with these straightforward, strategic planning steps, you're not just storing crypto, you're building a complete inheritance solution that is both incredibly secure and perfectly practical.
How to Set Up and Manage Your Multisig Wallet
https://youtube.com/watch?v=DOfN447yXOo
Let's move from theory to practice. Setting up a multisig wallet doesn't require you to be a technical expert; it's about thoughtful planning and being deliberate with your security. This guide will walk you through building a truly resilient system, putting you in direct control.
The journey starts by choosing the right tools for the job. You'll need two main components: multisig coordinator software and several hardware wallets. Think of the software as your command centre and the hardware wallets as the individual key-bearers who must sign off on any orders.
Choose Your Software and Hardware
First, you need to pick your coordinator software. Platforms like Sparrow Wallet and Nunchuk offer solid interfaces for creating and managing a multisig vault, but they leave you to figure out key distribution, backup strategy, and recovery planning entirely on your own.
That's where Evoke Multisig comes in. With Evoke, you hold two keys and we hold one in a 2-of-3 setup. You stay in full control of your funds at all times, but you get the added security of a professionally managed failsafe key. If you lose a device or need help with recovery, Evoke can step in as your co-signer. And because we only hold one key, we can never move your funds without you.
Next, you need the physical keys themselves. This is where hardware wallets come in. A crucial best practice is to use devices from different manufacturers. For example, you might combine a Ledger, a Trezor, and a Coldcard. This multi-vendor approach is your defence against any potential problem that might affect a single brand, like a firmware bug or a supply chain attack.
A secure multisig setup is built on diversity. By using different hardware brands alongside a trusted co-signing partner like Evoke, you eliminate single points of failure at both the physical and digital levels.
Once you have your tools in place, it's time to generate and back up your keys. This is arguably the most important part of the whole process.
Generate and Secure Your Keys
With your hardware wallets and software ready, you can begin the setup. The coordinator software will guide you in creating a new wallet, asking you to specify your chosen policy (like a 2-of-3). You’ll then connect each hardware wallet, one by one, allowing it to contribute its public key. The software uses these to construct your multisig wallet.
During this stage, each hardware wallet generates its own unique secret key and a corresponding 12 or 24-word recovery phrase. These recovery phrases are your ultimate backup. Securing them properly is non-negotiable.
Here are the best practices for backing up your recovery phrases:
Physical Backups: Consider engraving your seed phrases onto steel plates. Steel can survive a fire or a flood, ensuring your backups will too.
Geographic Separation: Never keep all your backups in one place. Store them in different, highly secure locations that are geographically separate. Think a safe at home, a safe deposit box at a bank, and perhaps another with a trusted solicitor.
No Digital Copies: Under no circumstances should you ever type your recovery phrases into a computer, take a photo of them, or save them in a password manager. They must remain completely offline. Always.
This physical separation of keys is the foundation of multisig security. It ensures no single disaster, like a burglary or a fire, can take out your entire setup.
Test, Test, and Test Again
Your wallet is created, and your backups are secured. You're not done yet. There is one final, essential step: testing. Before you transfer significant funds, you must verify that the system works and, more importantly, that you can recover your funds if things go wrong.
Perform a Small Test Transaction: Send a small amount of Bitcoin to your new multisig address. Then, go through the full process of creating and signing a transaction to send it back out. This confirms your hardware and software are working together correctly.
Conduct a Full Recovery Test: This is the most critical test. You need to simulate a disaster. Pretend one of your hardware wallets has been lost or destroyed. Use your steel backup of that device's recovery phrase to restore the key onto a brand-new hardware wallet. Then, confirm you can still sign a transaction using the restored key alongside another key from your setup.
Completing a full recovery test gives you incredible confidence. It proves your backups are correct and that your disaster recovery or inheritance plan is not just a theory—it’s a working, actionable strategy. This hands-on verification is what elevates a good security plan into a great one.
Your Top Multisig Questions, Answered
As you start exploring multisig, it’s natural for some practical questions to arise. Moving to a shared control model is a significant step, so it’s wise to get clear on the details before you begin. Here are some straightforward answers to the questions we hear most often.
Can I Use Different Brands of Hardware Wallets Together?
Yes, you absolutely can. In fact, we highly recommend it.
Combining hardware wallets from different manufacturers – say, a Ledger, a Trezor, and a Coldcard – is a security strategy known as multi-vendor multisig. This provides a powerful defence against any single point of failure at the company level.
By using devices from different brands, you insulate yourself from several key risks:
Firmware Bugs: A bug that affects one brand's software won't compromise the others.
Supply Chain Attacks: If one manufacturer’s production line is somehow compromised, your other keys are completely unaffected.
Company Viability: Your security doesn't depend on a single company staying in business forever.
Modern multisig coordinator software is designed to work smoothly with a range of hardware wallets, allowing you to build a truly resilient setup.
What Happens If a Key Holder Is Unavailable?
This is exactly the kind of problem multisig was designed to solve.
Let's imagine a 2-of-3 setup. You only need two of the three keys to authorise a transaction. If one key holder is travelling, uncooperative, or simply cannot be reached, you can still access and manage your funds with the remaining two keys.
The built-in redundancy of a multisig wallet ensures that the loss of a single key—or the unavailability of a single key holder—does not result in the loss of your assets. This is why a 2-of-2 setup is considered risky; it offers no such safety net.
Is a Multisig Wallet More Expensive?
There is a higher upfront cost, as you’ll need to buy multiple hardware wallets instead of just one. You might also notice that multisig transactions are slightly larger on the Bitcoin blockchain, which can mean marginally higher network fees when you send funds.
However, it's best to see this as an investment in security. When you weigh the minimal extra cost against the significant increase in security, resilience, and peace of mind, it’s a small price to pay. This is especially true if you’re securing a substantial amount of Bitcoin or building a robust inheritance plan.
How Do I Explain My Multisig Setup to My Family or Solicitor?
Keep your explanation simple. Your goal is to give them an actionable plan, not a lesson in cryptography. Focus on the ‘what’ and the ‘who,’ not the complex technical ‘how.’
Create a clear, straightforward document that outlines:
The Key Holders: List each person's name and their role in the setup.
The 'M-of-N' Rule: Explain it in plain English (e.g., "Any 2 of these 3 people are needed to move funds").
The Locations: Describe where the keys are stored in general terms (e.g., "in a bank safe deposit box," or "with our family solicitor").
The Expert: Provide contact details for a trusted technical guide who can walk them through the actual signing process when the time comes.
This approach gives your executor and family a simple, procedural map to follow. It ensures they can act confidently without getting bogged down by the technical side of things.
Managing digital inheritance requires clear planning, not just strong technology. Evoke Digital Solutions Ltd. provides a platform to create a solicitor-ready Digital Asset Schedule in minutes, documenting your multisig setup and recovery plan without ever asking for your private keys. Ensure your family has an actionable plan for your Bitcoin legacy. Learn more and secure your plan at https://evokevault.io.






